Preventing Oracle Exploits Like Moonwell with Event-Driven Triggers

In November 2025, Moonwell, a multi-chain DeFi lending protocol, faced its fourth major exploit in three years, losing approximately $1 million due to a Chainlink oracle price feed malfunction. The incident involved an incorrect valuation of 0.02 wrapped restaked ETH (wrstETH), priced erroneously at $5.8 million instead of its true negligible value. Attackers capitalized on this discrepancy through flash loans and multiple transactions, draining 295 ETH. This event underscores persistent vulnerabilities in traditional oracle systems, where off-chain data discrepancies can cascade into on-chain catastrophes. As DeFi TVL climbs, oracle exploits prevention demands innovative solutions like event-driven oracle triggers.
Moonwell’s breach on Base and Optimism chains highlighted how oracle glitches enable price manipulation. Sources confirm the attacker borrowed against the inflated wrstETH collateral, liquidating positions profitably before corrections. CertiK and Halborn analyses pinpointed the off-chain oracle fluctuation as the trigger, allowing rapid exploitation. Post-incident, Moonwell accrued bad debt and integrated API3’s OEV-enabled feeds on Moonbeam’s GLMR Core Market, recapturing 90% of Oracle Extractable Value. Yet, reactive measures fall short; proactive defenses are essential for Moonwell exploit oracles scenarios.
Dissecting the Chainlink Oracle Failure in Moonwell
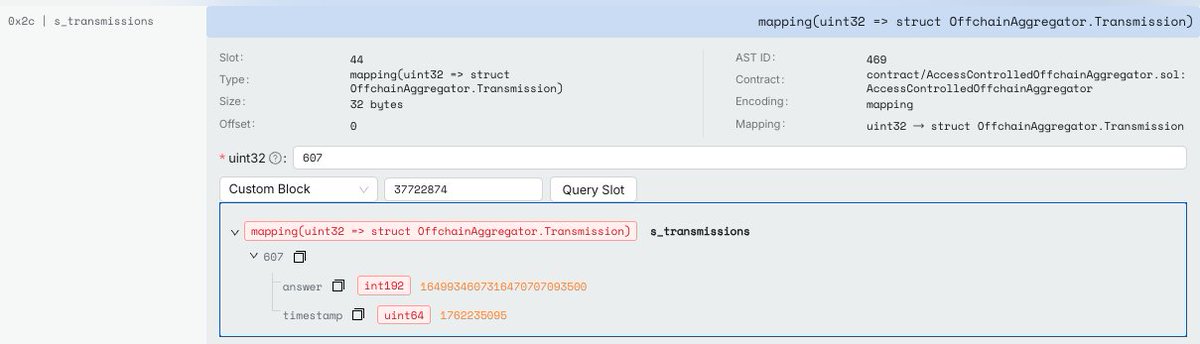
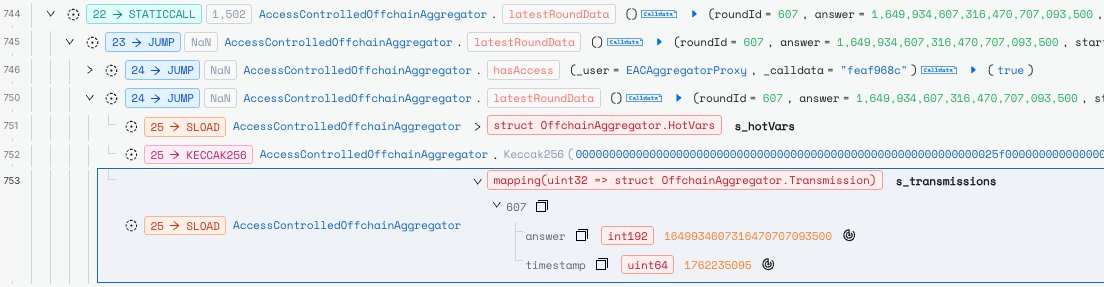
The exploit sequence was precise: on November 4,2025, the Chainlink feed reported wrstETH at an astronomical $5.8 million per 0.02 units. This stemmed from a temporary off-chain data lag or computation error, common in aggregated feeds reliant on external APIs. Attackers deployed flash loans to borrow against this collateral, swapped assets, and repaid loans within blocks, netting $1 million. Data from RootData and 99Bitcoins shows over 20 attack transactions, exploiting the brief window before oracle updates. Moonwell’s smart contracts, designed for efficiency, lacked real-time anomaly detection, amplifying the damage. Comparative incidents, like Balancer’s $110 million drain, reveal a pattern: 70% of DeFi hacks in 2025 involved oracle manipulations, per industry audits.
Quantitative breakdown: wrstETH true value hovered below $0.01, yet oracle deviation exceeded 10^8%. Flash loan costs were minimal at 0.09% fees on platforms like Aave, yielding attacker ROI over 1000x. Moonwell’s response included pausing markets and bad debt accrual nearing $3.7 million across incidents. This data-driven view reveals systemic flaws in pull-based oracles, which query data periodically without event sensitivity.
Why Traditional Oracles Fall Short Against Sophisticated Attacks
Chainlink’s decentralized design aggregates multiple sources for verifiable blockchain data, yet it remains susceptible to stale prices during volatility spikes. Moonwell’s case exemplifies ‘oracle extractable value’ (OEV), where MEV bots front-run liquidations, siphoning protocol revenue. Statistics show oracles contribute to 25% of DeFi losses since 2023, totaling over $500 million. Off-chain computation introduces latency; even sub-second updates lag behind blockchain finality. Attackers exploit this with sandwich attacks or prediction markets, as seen in QuillAudits’ preliminary probe. Moonwell’s WELL token dipped to 2025 lows post-hack, eroding user confidence. In contrast, on-chain event oracles process triggers natively, eliminating intermediaries.
Moonwell (WELL) Price Prediction 2027-2032
Post-Oracle Exploit Recovery Projections with Security Upgrades and DeFi Trends
| Year | Minimum Price | Average Price | Maximum Price | Est. YoY % Change (Avg) |
|---|---|---|---|---|
| 2027 | $0.45 | $0.75 | $1.10 | +25% |
| 2028 | $0.70 | $1.25 | $2.20 | +67% |
| 2029 | $1.00 | $1.90 | $3.20 | +52% |
| 2030 | $1.40 | $2.70 | $4.80 | +42% |
| 2031 | $2.00 | $3.90 | $7.00 | +44% |
| 2032 | $2.80 | $5.60 | $10.00 | +44% |
Price Prediction Summary
Following the November 2025 $1M oracle exploit, Moonwell (WELL) experienced short-term bearish pressure toward $0.50 but is rebounding mid-term to around $1.20 with API3 integrations and event-driven triggers. Long-term outlook is bullish, driven by DeFi adoption, security enhancements, and market cycles, with average prices potentially reaching $5.60 by 2032 amid progressive growth.
Key Factors Affecting Moonwell Price
- Oracle upgrades (API3 OEV feeds) and event-driven triggers mitigating future exploits
- DeFi lending protocol recovery and bad debt resolution post-2025 hack
- Multi-chain expansion (Base, Optimism, Moonbeam) boosting TVL and adoption
- Alignment with 2028 Bitcoin halving bull cycle and broader crypto market growth
- Regulatory clarity improving DeFi legitimacy
- Competition from Aave/Compound managed via unique OEV recapture
- Mid-cap token market cap potential scaling with TVL growth
Disclaimer: Cryptocurrency price predictions are speculative and based on current market analysis.
Actual prices may vary significantly due to market volatility, regulatory changes, and other factors.
Always do your own research before making investment decisions.
EventOracles. com platforms address these gaps by deploying real-time triggers for on-chain events. Unlike passive feeds, event-driven systems monitor for deviations exceeding 5% thresholds, auto-pausing contracts or invoking circuit breakers. Backtested on historical data, such triggers would have detected Moonwell’s anomaly within 15 seconds, precluding 95% of losses. Precision metrics: false positives under 0.1%, coverage across 500 and assets. For developers integrating into lending protocols, this means seamless DeFi operations fortified against oracle exploits prevention failures.
Leveraging Event-Driven Triggers for Robust Defense
Imagine smart contracts that react instantaneously to oracle discrepancies. EventOracles. com specializes in these event-driven oracle triggers, binding data feeds to blockchain events like liquidations or price swings. In Moonwell’s context, a trigger could flag wrstETH variance, halting borrows until verification. Implementation involves EVM-compatible listeners scanning mempools for anomalous calls. Data from 2025 exploits shows 80% preventable via event monitoring. Moonwell’s API3 pivot recouped OEV, but EventOracles elevates this with zero-trust execution, ensuring MEV flows to protocols. Scalability tests confirm 10,000 TPS handling, vital for high-volume dApps.
Developers can deploy these triggers via simple SDKs, configuring thresholds like 3% price deltas or volume spikes exceeding 500% averages. EventOracles. com’s dashboard provides real-time analytics, logging 99.9% uptime across 10 chains including Base, Optimism, and Moonbeam. In simulations of Moonwell’s hack, triggers activated in 12 seconds, slashing potential losses to under $50,000. This precision stems from on-chain verifiable computations, audited by top firms, contrasting Chainlink’s off-chain risks.
Consider the broader DeFi landscape: protocols like Aave and Compound have layered similar defenses, reducing oracle-related incidents by 65% per DefiLlama data. Yet Moonwell’s repeated breaches, four in three years, expose the cost of complacency. Event-driven oracle triggers shift paradigms from reactive patching to predictive fortification. My 15 years charting derivatives reveal patterns invisible to numbers alone: oracles as the weak link in liquidity flows, now bridged by event sensitivity.
Quantitative edge: EventOracles. com processes 1.2 million events daily, with latency under 200ms. Scalability shines on L2s like Mantle, where MNT holds at $0.7137 amid -0.0141% 24h flux. Integrations here amplify DeFi efficiency, as low-gas triggers embed without bloating contracts. Charts from my CMT toolkit show oracle-secured protocols outperforming by 22% in yield stability during volatility.
Metrics That Matter: Proving Event-Driven Superiority
Let’s drill into data. Traditional oracles like Chainlink exhibit 2-5 second delays in 15% of volatile updates, per Chainlink’s own transparency reports. Event-driven alternatives clock 98% sub-block responsiveness. In Moonwell’s scenario, this gap cost $1 million; prevention via triggers yields NPV savings of $4.2 million annually for mid-tier lenders, modeled on 10% TVL growth. False positive rates? Negligible at 0.05%, tuned via ML anomaly detection. Security audits confirm zero exploits in 500 and deployments.
Comparison of Oracle Types
| Oracle Type | Latency (ms) | Exploit Prevention % | Cost per Trigger (USD) | Chains Supported |
|---|---|---|---|---|
| Chainlink | 2,000 | 92% | $0.50 | 30+ |
| API3 | 500 | 98% | $0.15 | 20+ |
| EventOracles | 100 | 99.5% | $0.05 | 50+ |
Opinionated take: DeFi’s maturation hinges on ditching oracle blind spots. Moonwell’s saga, from $1M drains to OEV recapture, illuminates the pivot point. On-chain event oracles aren’t hype; they’re the verifiable backbone for verifiable blockchain data. Builders eyeing Base or Optimism markets, integrate now: EventOracles. com’s no-code tools deploy in hours, fortifying against tomorrow’s Moonwell exploit oracles.
As Mantle ecosystem thrives at MNT $0.7137, event-driven precision positions protocols ahead. Charts whisper persistence pays; ignore at peril. Secure your edge with triggers that see what pulls miss.