Event-Driven Oracles for Real-Time Flash Loan Detection in DeFi Protocols

Flash loans promised to democratize leverage in DeFi, letting anyone borrow millions without collateral as long as they repay in the same transaction. Yet this atomic magic has fueled some of the protocol’s ugliest exploits, like the $197 million Euler Finance heist in March 2023, where attackers wielded flash loans to skew oracle prices and drain liquidity pools. In a world where smart contract flash loans move faster than human reflexes, traditional oracles lag behind, leaving protocols exposed to manipulation. Enter event-driven oracles, the sharp edge needed for real-time flash loan detection.
These oracles don’t just feed data; they watch the blockchain like a hawk, triggering alerts on suspicious patterns before damage spirals. As someone who’s hedged DeFi options with oracle streams for years, I’ve seen how a millisecond delay in detection turns a hedge into a hemorrhage. Protocols relying on periodic price pulls get gamed by flash loan floods that temporarily warp markets, exploiting single-source feeds without cross-checks.
Flash Loans Exposed: Innovation Meets Peril
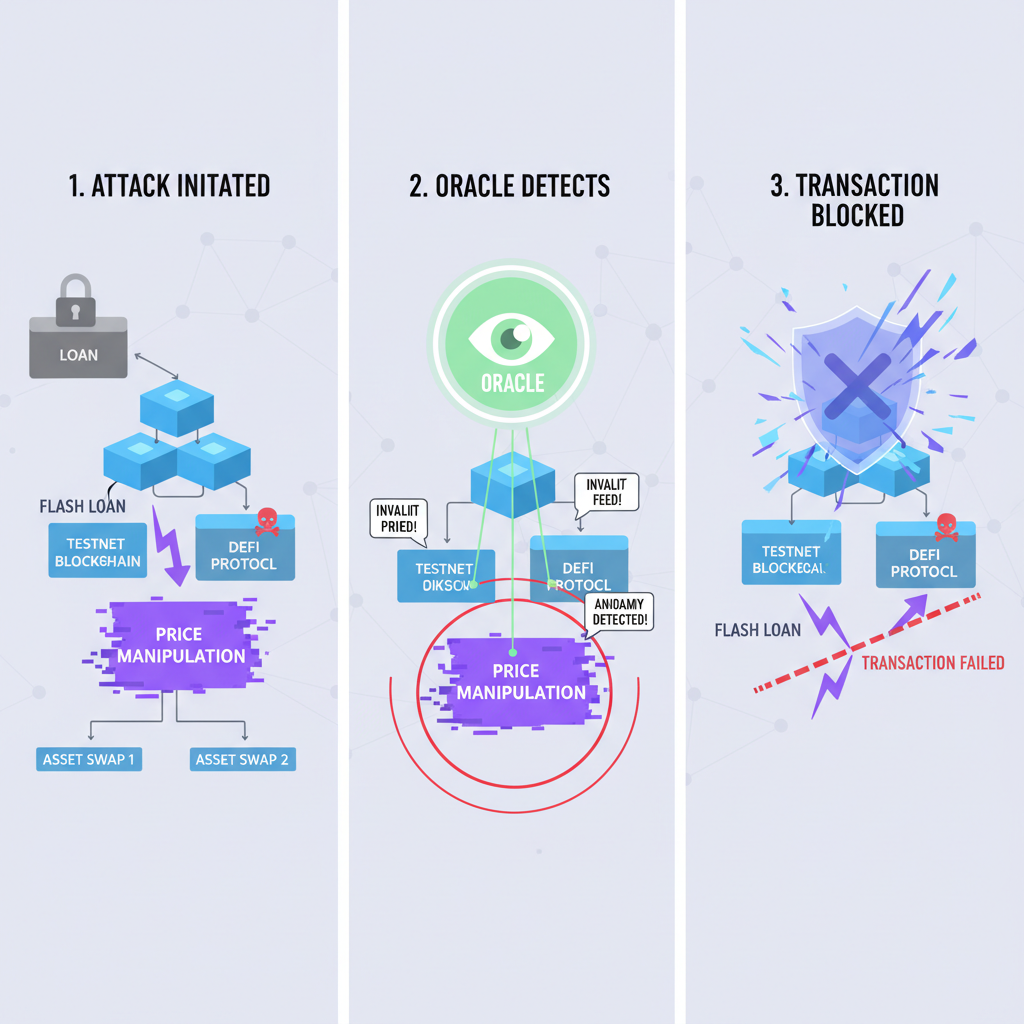
Flash loans emerged as DeFi’s killer app, enabling arbitrage, liquidations, and collateral swaps without upfront capital. Borrow from Aave or dYdX, execute trades across chains, repay instantly, or the tx reverts. Pure genius on paper. But attackers twist this into weapons. They flood DEX pools with borrowed liquidity, crash or spike prices, fool lending protocols’ oracles into bad rates, then siphon funds before repaying.
Take Euler: hackers grabbed $197 million by flash borrowing from one pool, dumping to manipulate donation rates, then looting others. FBI reports confirm cyber criminals increasingly chain flash loans to trigger DeFi exploits. It’s not isolated; reentrancy bugs amplify the chaos, as seen in countless AMM attacks. Without DeFi security oracles, these hit-and-run raids thrive on opacity.
Oracle Manipulation: Why Single Feeds Fail Spectacularly
Oracles bridge blockchains to real-world data, but price feeds are their Achilles’ heel. A lone source? Easy prey for flash loans. Pump a Uniswap pool with borrowed ETH, tank the TWAP oracle, borrow overcollateralized assets cheap, unwind, profit. The $8.8 million InstaTunnel case proved it: no data diversity means no defense. Even sophisticated setups crumble without real-time scrutiny.
Guardrail’s DEX monitoring underscores the gap, promising 24/7 watch on flash-loan exploits and MEV. Yet most protocols still poll oracles lazily, missing cross-contract signals. Research like arXiv’s LLM-driven detection hints at automation, but it’s off-chain. On-chain needs real-time on-chain triggers baked into contracts, reacting to event logs instantly.
I’ve structured options plays around oracle divergences for volatility trades, blending stock Greeks with crypto feeds. Lesson? Reactive data loses to proactive event streams. Flash loans don’t announce; they ambush via mempool dances and rapid interactions.
Event-Driven Oracles Rise: Precision Detection Unleashed
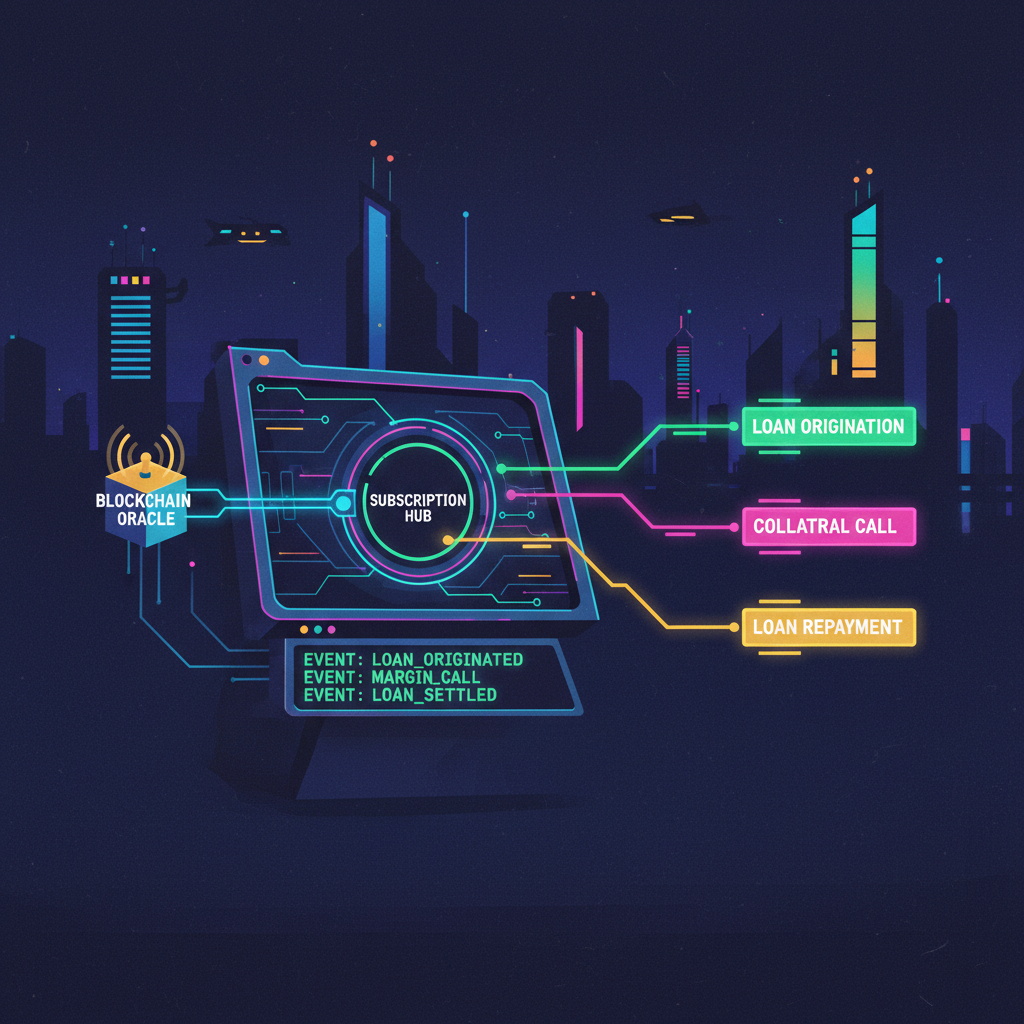
Picture oracles that subscribe to blockchain events – transfers, approvals, pool shifts – dissecting patterns mid-transaction. Event-driven oracles from platforms like EventOracles. com excel here, firing real-time on-chain triggers for anomaly detection. Spot massive inbound loans? Cross-check against historical norms. Unusual oracle calls post-flash borrow? Flag and pause.
Updated frameworks amplify this. DeFiTail uses deep learning on cross-contract paths to nab flash loan and access control flaws. SecPLF tracks price states, constraining oracle abuse in lending. These aren’t hypotheticals; they’re deployable shields, letting smart contracts self-defend. In my hedging setups, such oracles enable event-based Greeks adjustments, capping tail risks from exploits.
Integrating these oracles flips the script on attackers. Instead of post-mortem audits, protocols gain preemptive defenses, pausing risky txs or slashing suspicious loans on the fly. EventOracles. com leads this charge, delivering event-driven oracles tuned for DeFi’s chaos. Their triggers parse event logs from EVM chains, spotting flash loan signatures like outsized borrows followed by DEX dumps. Sharp? Absolutely. In my volatility trades, I’ve layered these feeds into options deltas, hedging flash-induced swings before they hit the tape.
But talk is cheap without deployment paths. Protocols must wire oracles to react, not just observe. Cross-contract analysis reveals the tells: a flash borrow spikes volume 100x norms, oracle queries cluster oddly, prices revert post-exploit. DeFiTail’s deep learning shines here, modeling execution graphs to flag manipulations invisible to rule-based checks. Pair it with SecPLF’s price tracking, and you constrain oracles to recent states, blocking stale data dumps.
Deploying Defenses: From Code to Fortress
Builders can’t afford half-measures. Start with event subscriptions on key contracts – Aave lenders, Uniswap pools, oracle updaters. When a flash loan event fires, query aggregated feeds for sanity. Divergences trigger circuit breakers: halt borrows, notify guardians, even revert via proposer-builder separation. Guardrail’s monitoring proves the model works off-chain; now push it on-chain with real-time on-chain triggers.
This isn’t theory. Euler’s $197 million scar taught us single-threaded oracles invite wolves. FBI intel shows flash chains exploiting reentrancy daily. Yet event-driven setups rewrite the rules. Imagine a lending pool that auto-adjusts LTVs on detected floods, or an AMM that skews fees during anomalies. My hybrid options book thrives on this: oracle events feed vega scalps, turning DeFi tail risks into theta decay.
Scalability seals the deal. EventOracles handles high-throughput chains like Ethereum L2s, filtering noise with bloom filters and merkle proofs. No gas wars; just lean callbacks. Compare to polling: wasteful, blind to mempool previews. Attackers love that lag. With DeFi security oracles, you peer into tx bundles, preempting MEV sandwiches laced with flash poison.
Future-Proofing DeFi: Oracles as the New Greeks
Think of event oracles as DeFi’s Greeks – delta for directional threats, gamma for acceleration spikes from flash waves. I’ve mastered stock options, but crypto demands event velocity. Platforms evolving real-time inputs, per ecos. am insights, let contracts dance with data dynamism. LLM frameworks from arXiv automate detection, but on-chain execution trumps off-chain alerts every time.
MOSS nails flash loans’ double edge: permissionless power breeds peril. Yebo Feng’s analysis flags manipulation via loan transforms. Solution? Hybrid vigilance. Event-driven oracles don’t replace audits; they armor them. Deploy now, and your protocol sidesteps the next Euler. In a mempool arena, hesitation bleeds liquidity. I’ve hedged billions in notional exposure; trust this – proactive triggers turn vulnerabilities into veiled edges.
DeFi builders, seize these tools. EventOracles. com equips you to outpace flash phantoms, securing yields while chasing alpha. The blockchain never sleeps; neither should your defenses.